A highly hackable US biodefense system
By Elisabeth Eaves | December 19, 2018
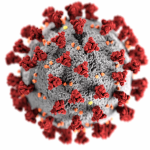
 (Photo credit: Vinicius Munhoz via Creative Commons.)
(Photo credit: Vinicius Munhoz via Creative Commons.)
A US system to detect biological attacks has had a variety of well-documented problems over its 15-year life span, from mistakenly reporting non-existent germ attacks to taking too long to collect and analyze samples. Reporting by Defense One suggests it has another one, too: insecure data.
After the anthrax attacks of 2001, the government wanted a way to tell when airborne pathogens were on the loose, and in 2003 launched what President George W. Bush called “the nation’s first early-warning network of sensors to detect biological attack.” Operating in more than 30 cities, BioWatch gathers air samples, sends them to labs, and analyses them for DNA that would indicate a toxin or pathogen. But the program, which has cost more than $1 billion so far, turned up false positives and can take upwards of a day to report results. Earlier this fall, a Department of Homeland Security official said BioWatch would be replaced within the next couple of years.
Until then, it’s a first line of defense against bioterrorism. But as Defense One reports, the website that BioWatch uses to coordinate between health workers and government officials (called biowatchportal.org) is insecure, according to both the Department of Homeland Security inspector general and a former department employee. With access to the website, an adversary could find the sensor locations where air samples are gathered, target the professionals using it, or presumably simply take it offline.
Former Homeland Security employee Harry Jackson, whose findings were later validated by the inspector general, published his recommendations last year, and they will sound depressingly familiar to ordinary folks worried about hacking. The system “designed to reduce the loss of life in the event of an act of bioterrorism,” Harry Jackson wrote, “should certainly, at a minimum, have a trusted Internet connection and require two-factor authentication.”
Publication Name: Defense One
To read what we're reading, click here
Together, we make the world safer.
The Bulletin elevates expert voices above the noise. But as an independent nonprofit organization, our operations depend on the support of readers like you. Help us continue to deliver quality journalism that holds leaders accountable. Your support of our work at any level is important. In return, we promise our coverage will be understandable, influential, vigilant, solution-oriented, and fair-minded. Together we can make a difference.
Topics: Biosecurity, What We’re Reading