Biden to private sector: Cybersecurity is your responsibility—not the user’s
By Brandon Kirk Williams | May 1, 2023
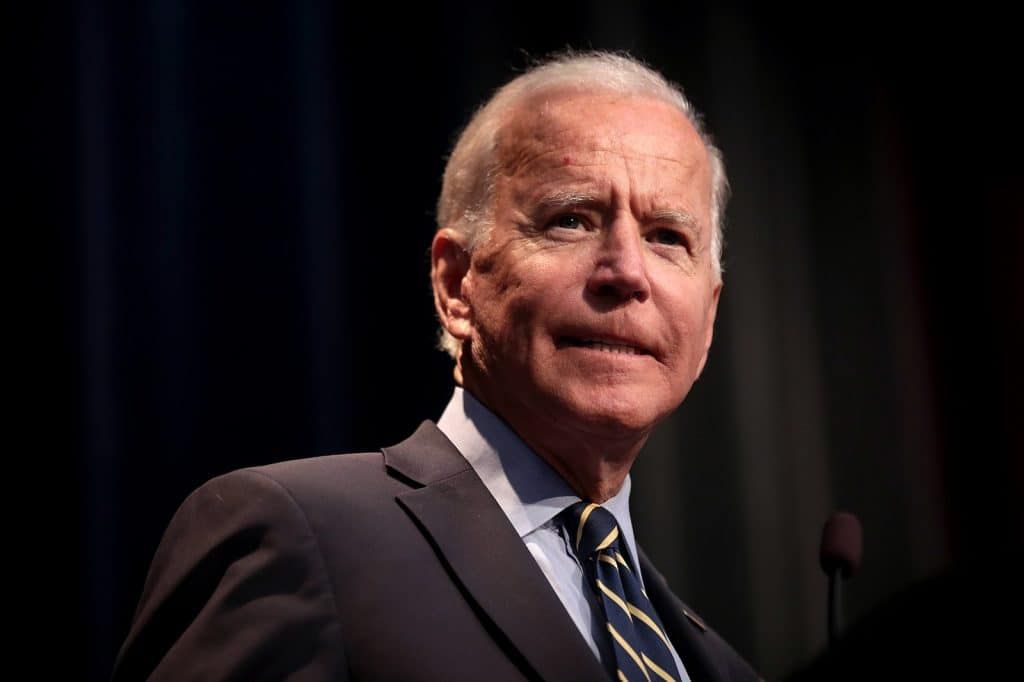 Joe Biden. Credit: Gage Skidmore. Accessed via Wikipedia. CC BY-SA 2.0.
Joe Biden. Credit: Gage Skidmore. Accessed via Wikipedia. CC BY-SA 2.0.
The Biden administration’s recently-released National Cyber Strategy proposes a new social contract that places the responsibility of protecting the nation’s cybersecurity on the private sector, not individual users. The novel model for national cyber resilience, which overturns decades of cybersecurity practice, is the result of an impending avalanche of disruptive technological threats that will eclipse the ability of everyday citizens and small businesses to protect data. No longer can the country rely on a model where private sector vendors and suppliers push security onto users. The National Cyber Strategy pledges to use government power to realign incentives and shape markets—by using carrots of government funding and sticks of regulation—to forge a new social contract for cybersecurity at a transitional moment.
Unlike previous such strategies, the new National Cyber Strategy rebalances responsibility to generate a new social contract for a resilient national cybersecurity to counter threats from malicious nations and emerging technology. Only the private sector can embed security-first product development to protect the country’s information architecture from the converging threats of the modernizing internet, quantum computing, and the hyper-connected Internet of Things (IoT), a network of physical objects, or “things,” connected to the internet that ranges from pacemakers to home ovens. In its call for new principles for cyber resilience, the document overturns decades of accepted practice for the private sector and constraints on government. It moves beyond rhetoric to declare that government must utilize its authorities to correct misaligned incentives that will jeopardize a flourishing digital ecosystem—a striking proposition.
Now-retired National Cyber Director Chris Inglis coordinated the writing of the Biden administration’s document. This is the first such document prepared by a national cyber director, and this version stands above all previous cyber strategies. Inglis and his team structured the document around five pillars, two of which—”Shape Market Forces to Drive Security and Resilience” and “Invest in a Resilient Future”—are most remarkable for outlining a new direction for cyber. The other pillars contain noteworthy changes, but nothing near the ruptures of those two, known as pillars three and four.
Pillar three. In this section, titled “Shape Market Forces to Drive Security and Resilience,” the documentunambiguously states that current market dynamics have failed to reduce threats and incentivize vendors and suppliers to put secure-by-design principles in the foreground when rolling out products. Stewards of data, the strategy insists, bear the responsibility for safeguarding information against malicious actors. The private sector owns and operates the majority of the nation’s internet; risk mitigation for data theft, poor design, and vulnerabilities therefore should fall on industry. But until now, industry has possessed little incentive to ensure that a foundation of security is firmly established, even were it to slow the growth of the Internet of Things or a software release.
The result is a digital ecosystem that’s ill prepared for a future of metastasizing threats.
The Biden cyber team, however, did not pen an anti-capitalist screed. Pillar three emphasizes that “market forces remain the first, best route to agile and effective innovation,” but it acknowledges that jockeying for market share has come at the expense of the United States’ economy and national security. The solution? Guiding the market via incentives and regulation to guarantee that security remains at the heart of innovation—before technological threats compound and vandalize the country’s digital ecosystem.
The Biden administration’s threat perception is shaped by the systemic risks posed by an explosion of Internet of Things vulnerabilities and by software that neglects basic best security practices. From households to critical infrastructure to health devices, little in the United States will go untouched by the Internet of Things in coming decades. Proliferating Internet of Things devices multiply the attack surfaces that threat actors can target for data exfiltration, hijacking for botnets, or to surveil users. Dell projects that 41.6 million internet-connected devices will be operational in 2025, and usage estimates climbs year-after-year. Internet of Things vendors often elevate deployment over security. Everyday consumers possess scant ability to manage upgrades or have full knowledge of limited liability that is often buried in contracts. Similarly, software designers and vendors are encouraged to rush products to market without safety assurances for users. The lack of uniform testing protocols, or clarity on third-party inputs, leaves users susceptible to risk; and little evidence exists that the market will correct for negligence in software or Internet of Things.
Pillar three endorses a stronger federal presence and regulation to overcome the lax oversight that allowed vulnerabilities to flourish at the expense of protecting users. The administration’s prescriptions include transparent labeling for internet-connected devices, updated government procurement policies, and software liability legislation. The latter is most far-reaching but would also provide an option for companies to adopt—a software safe harbor—that establishes best design and development practices. Utilizing a software safe harbor would shield companies from legal action, provide users with the knowledge of vendors that meet standards, and steer innovation. Instead of depicting regulation as a burden that stifles the market, the strategy’s authors insist that government oversight nourishes a healthy innovation ecosystem. In this sense, the state is exercising its power to realign the mismatch between public and private interests while also providing users with the agency to influence industry.
Pillar four. “Invest in a Resilient Future” envisions how government can leverage federal spending to prepare for a transition to a new era of both technological threat and opportunities. This part addresses the gap between public and private capital that leaves the country vulnerable as it anticipates challenges to the foundation of the internet, quantum technologies, and nation-wide electrification. Pillar four identifies the necessity of federal initiatives to ensure citizens can rely on secure infrastructure—ranging from information architectures to the electrical grid—that the private sector will not fund, because only the government can fill the gap.
The fourth pillar identifies three foundational threats that require federal investment: the internet’s evolving network ecosystem, post-quantum encryption, and a resilient-by-design electrical grid. Although the private sector owns the bulk of the internet, modernizing governmental networks can create momentum to alter the nation’s internet. The baseline domains and protocols undergirding the internet are currently updating to a more secure space with fewer attack surfaces. Internet Protocol version 6 (IPv6) is replacing its legacy predecessor version 4. (Internet protocols govern how data is transmitted and received across networks.) The National Security Agency’s guidance for mitigating threat in the transition from Internet Protocol version 4 to Internet Protocol version 6 stresses that the former is inadequate for the expanding number of devices that will require connectivity.
The latest cyber strategy’s authors also adopt a medium-term view on the future of post-quantum cryptography. Recognizing the vulnerabilities in the transition to quantum computing, pillar four pledges that government will accelerate its funding of basic research and development of cybersecurity solutions. A fully operational quantum computer that can compromise standard RSA encryption (algorithm for secure data transition) could be 10 years away. Or it could arrive in six years, according the Cloud Security Alliance’s countdown. Preparing for that future, as the authors assert, benefits from government initiative. Post-quantum cybersecurity will necessitate government-wide standardization alongside industry adoption of the National Institute of Standards and Technology’s (NIST) post-quantum algorithms. The Biden administration should be credited for ushering the country toward achieving post-quantum cryptographic agility. Transitioning to post-quantum cybersecurity, as with energy, demands that government offer remedies that ensure the private sector is acting to protect users.
Widespread electrification, similarly, requires cybersecurity standardization for the coming tide of new energy storage, generation, and transmission. Biden’s cyber team recognizes that foregrounding cyber resilience into energy infrastructure at the dawn of an energy transformation is a weighty task. National Labs and the Department of Energy will spearhead the effort to prevent states and the private sector from implementing a “patchwork of security controls” without necessary cybersecurity for devices and sensors. The technical solution, however, hinges on government preserving its funding of research and development to steer the market toward creating secure opportunities for users.
Pillar four zooms in to fix “innovation without security” with the smart application of federal power, including spending. Government’s reassertion of its agency in shaping the innovation ecosystem has been a priority of the Biden administration. Two laws—the Inflation Reduction Act and the CHIPS and Science Act—exemplify how the Biden administration views the urgency of government returning to its Cold War-era championing of innovation. The Cyber Strategy spells out funding priorities and documents how a bevy of government institutions are poised to implement a new cyber social contract: the National Science Foundation, NIST, the Department of Energy and its complex of National Labs, and Federally Funded Research and Development Centers. By harmonizing ways, means, and ends, Inglis’s team advocates for a cyber social contract that promotes innovation.
The genesis of the strategy’s new cyber social contract was detailed in Inglis’s and Harry Krejsa’s Foreign Affairsarticle “The Cyber Social Contract: How to Rebuild Trust in a Digital World.” The authors noted that misaligned incentives against a backdrop of cyber volatility left the nation, the private sector, and citizens at persistent risk. National security and citizens’ daily lives were imperiled without a reset, they wrote. Impending waves of digitization would embolden malicious actors to prey upon the staggering number of vulnerabilities. “With a shared and affirmative vision, the public and private sectors can build a new social contract,” the authors insisted, “without undermining the integrity and vitality essential to an innovative economy.”
How does the blueprint in the Foreign Affairs article differ from the administration’s cybersecurity strategy document? Inglis and Krejsa avoid a discussion of responsible regulation, as public interest technologist Bruce Schneier commented. Schneier lauded the article but tempered his praise by asserting that “regulation is how society aligns market incentives with its own values.” Without explicitly foregrounding the state’s power to wield a regulatory hammer, Inglis and Krejsa cannot fully embrace the fundamental element of state authority in crafting a new social contract for cybersecurity. The National Cyber Strategy, on the other hand, lays the foundation for modernizing how users, the private sector, and the state interact in the domain.
The strategy includes other notable changes, including the absence of any mention of deterrence and escalation that signals a victory for the adherents of Defend Forward—a strategy that intends to “disrupt or halt malicious cyber activity at its source.” For years, General Paul Nakasone the dual-hatted Director of the National Security Agency and Commander of U.S. Cyber Command led a campaign to dislodge traditional deterrence theory from cyber strategy. Richard Harknett and Michael Fischerkeller’s 2017 “Deterrence is Not A Credible Strategy for Cyberspace” argued against voices who applied deterrence thinking to the nation’s cybersecurity. Debates over deterrence persisted. The Cyberspace Solarium Commission formulated a strategy of layered cyber deterrence that welded Defend Forward onto its framework to restore deterrence. Ultimately, as evidenced in the cyber strategy document, deterrence is inadequate to tackle the gravity of technological threats that malicious actors will capitalize on.
The document serves as a testament to the foresight of the U.S. Cyberspace Solarium Commission’s recommendation to stand up the National Cyber Director’s office. Inglis’s former office possesses the centralizing force to harmonize disparate interagency interests. The National Cyber Director recruits staff from across the government, private sector, and academia to obtain a 360-degree view of the threat landscape. Future administrations will likely turn to the National Cyber Director to publish cyber strategies that maintain the technical acumen and policy smarts in the 2023 report. The accomplishment, however, is less about the bureaucratic capabilities than the Cyber Strategy’s ability to imagine a new operating dynamic for the nation’s cybersecurity. Former Director Inglis and his staff are to be applauded for this sophisticated document.
Obstacles are present, most prominently one that involves how the private sector may resist regulation that could impede commercialization of new technologies. The reigning incentive structure rewards quick commercialization where security ranks below rushing products to market. Realigning priorities will require consistency across the Biden administration and subsequent presidencies that build upon experiences forged over the past year.
Pathways for collaboration improved as a result of the close public-private cooperation after the Russia-Ukraine War’s onset in 2022. Anne Neuberger, the Deputy National Security Adviser for Cyber and Emerging Technology, described it as “a coming-of-age for our cyber community.” Forging a new social contract for cyberspace after ransomware attacks like the 2021 Colonial Pipeline incident, high profile hacks, and the shift to cyber intrusion data sharing intersects with new threat awareness after the start of Russia’s invasion of Ukraine.
In this milieu, the Biden administration is employing the power of government to renegotiate the rules of cybersecurity. The National Cyber Strategy articulates a bold vision for renovating the cyber social contract, and action is necessary if not overdue. Attack surfaces that malicious actors and nations such as China and Russia will target are increasing at a staggering rate. Untenable risks require government intervention to align incentives and guarantee users are not prey due to the private sector’s errors. This administration and subsequent ones will face consistent cyber volatility. Action soon will ward off the market failures that endanger the nation’s digital ecosystem that is the woven into the fabric of Americans’ daily lives. A new cyber social contract is overdue, and it prepares the nation for the inescapable threats ahead.
The opinions are those of the author and do not necessarily represent the opinions of Lawrence Livermore National Laboratory, Lawrence Livermore National Security, LLC, the Department of Energy, the National Nuclear Security Administration, the United States government, or the Wilson Center.
Together, we make the world safer.
The Bulletin elevates expert voices above the noise. But as an independent nonprofit organization, our operations depend on the support of readers like you. Help us continue to deliver quality journalism that holds leaders accountable. Your support of our work at any level is important. In return, we promise our coverage will be understandable, influential, vigilant, solution-oriented, and fair-minded. Together we can make a difference.














“Only the private sector can embed security-first product development to protect the country’s information architecture from the converging threats of the modernizing internet” That’s right, depend on the private sector to protect the country…just like the private financial sector protected the global economy. I will bet whoever is pushing this has or will have a financial conflict of interest that compromises national security. Such a shame to see The Bulletin publishing such bad ideas.
“Now-retired National Cyber Director Chris Inglis coordinated the writing of the Biden administration’s document.” Before his approval to become National Cyber Director, Inglis worked for WestExec Advisors. A 2021 investigation by The American Prospect found that Inglis “earned $15,000 from the firm and worked for internet security outfit CrowdStrike and email encryption company. And we all know how creditable CrowdStrike turned out to be. This is like a bad joke.