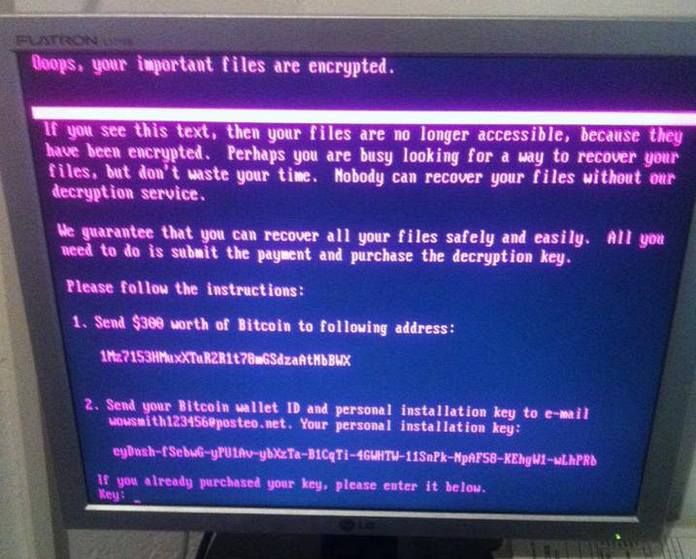
 NotPetya initially disguised itself as ransomware with messages demanding payment. Photo by Eugene Bouquet / Creative Commons.
NotPetya initially disguised itself as ransomware with messages demanding payment. Photo by Eugene Bouquet / Creative Commons.
Even this far into the information age, it can be hard to really picture what cyberwarfare looks like. Hundreds of attacks, thousands of targets, and millions of dollars in damage can all sound like so many ones and zeros. So thanks go to Wired senior writer Andy Greenberg, whose September cover story about “the most devastating cyberattack in history” gives a sense of what it felt like to be a victim of NotPetya, a piece of malware that Russian military hackers released on the world via Ukraine.
By the middle of 2017, Ukraine was already a “scorched-earth testing ground for Russian cyberwar tactics.” Then Moscow released NotPetya. First it upended lives in Ukraine, hitting hospitals, power companies, airports, banks, card payment systems, federal agencies, and computers used at the Chernobyl nuclear cleanup site. The cyberweapon then spread to major companies all over the world. It caused more than $10 billion in total damage as it strafed drug maker Merck, delivery company FedEx, and Russia’s own oil producer Rosneft, among many others.
Greenberg takes a deep-dive look at the impact on the Danish-headquartered global shipping company Maersk, infected via a single computer in its Odessa office. Computers in Copenhagen suddenly went dark. At shipping terminals around the world, 18-wheelers backed up by the hundreds. As customers frantically tried to move their stranded goods, staff and consultants worked around the clock to recover. Basically, a section of the global supply chain on which we all depend was briefly shut down. And as Greenberg writes, almost everyone who has studied NotPetya agrees on one point: “that it could happen again or even reoccur on a larger scale.”
Publication Name: Wired
To read what we're reading, click here
Together, we make the world safer.
The Bulletin elevates expert voices above the noise. But as an independent nonprofit organization, our operations depend on the support of readers like you. Help us continue to deliver quality journalism that holds leaders accountable. Your support of our work at any level is important. In return, we promise our coverage will be understandable, influential, vigilant, solution-oriented, and fair-minded. Together we can make a difference.
Keywords: cyber weapons
Topics: Cyber Security, What We’re Reading











However, Mr. Greenberg’s article that Ms Eaves is referring to does not present the slightest evidence to support his claim that NotPetya was launched by or for the Russian government. And since he repeats long-since debunked stories such as “Russian hackers cracked the DNC servers”, and thinks Fancy Bear is the name of a group, rather than of a set of software, his claims should be treated with considerable skepsis.